- Written by Ataullah Wali
Introduction
Ransomware has changed. Modern attacks no longer focus only on encrypting production systems. They actively search for backup repositories, privileged accounts and recovery infrastructure before launching encryption. This is why immutable backup has become one of the most important technical controls in modern IT resilience planning. Without immutability, your backup environment may be compromised at the same time as your production systems. For IT managers responsible for protecting data, maintaining uptime and meeting recovery objectives, understanding how immutable backup works is no longer optional. It is essential.
Is your quote fair?
Don't sign that contract yet. Check stock & price with Qual first.
What Is Immutable Backup?
Immutable backup refers to backup data that cannot be altered, encrypted or deleted for a defined period of time, even by administrators.
The key concept behind immutable backup is write-once-read-many (WORM) storage. Once data is written, it becomes locked for a retention period.
During that time:
- It cannot be modified
- It cannot be deleted
- It cannot be overwritten
- It cannot be encrypted by ransomware
Even if an attacker compromises admin credentials, immutable backup prevents destruction of recovery data.
For IT managers, immutable backup is not just a storage feature. It is a defensive control within a wider resilience architecture.
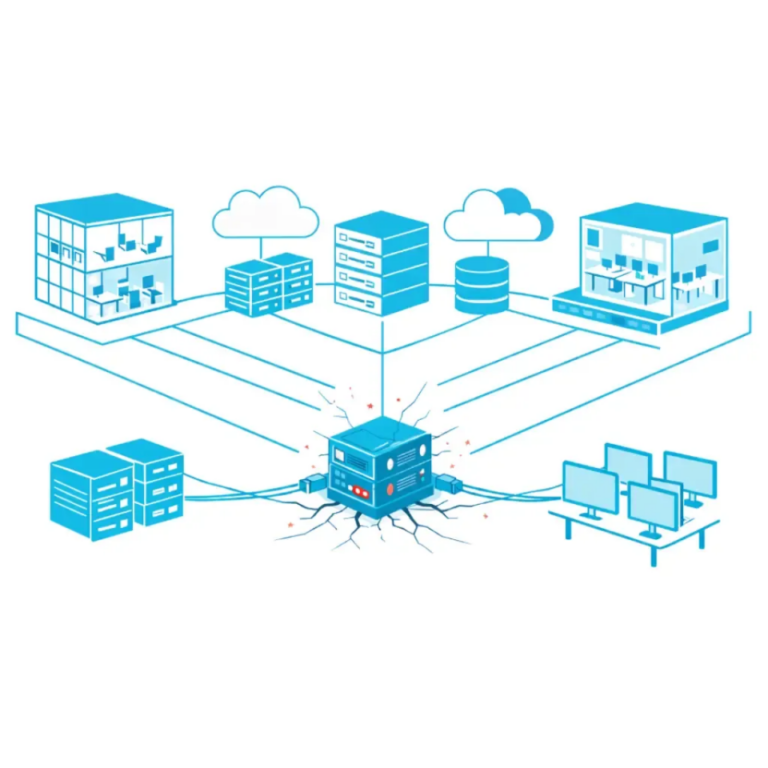
Why Traditional Backup Fails Against Ransomware
Traditional backup models were designed for hardware failure and accidental deletion.
They were not designed for deliberate attack.
Modern ransomware operators typically:
- Gain privileged access
- Disable security monitoring
- Locate backup repositories
- Delete or encrypt backups
- Launch encryption payload
If backup storage is network-accessible and admin-controlled, it becomes vulnerable.
Without immutable backup, attackers can:
- Delete backup chains
- Corrupt restore points
- Disable retention
- Remove snapshots
This leaves organisations with no clean recovery path.
Immutable backup prevents this scenario because data cannot be altered within its retention window.
How Immutable Backup Works Technically
To implement immutable backup correctly, IT managers must understand the underlying mechanisms.
Immutable backup is typically delivered through:
- Object storage with retention lock
- Immutable blob storage
- Hardened Linux repositories
- Air-gapped systems
- Snapshot locking
Object Storage with Retention Lock
Object storage platforms (such as S3-compatible systems or Azure Blob Storage) support object lock features.
When immutable backup is configured:
- Backup data is written as objects
- A retention policy is applied
- The object is locked until the retention date expires
Even administrators cannot override this lock in compliance mode.
Time-Based Retention
Immutable backup uses time-based retention.
For example:
- 14-day immutability
- 30-day immutability
- 90-day immutability
This means restore points within that window are protected.
If ransomware is discovered, recovery can occur using protected restore points.
Air-Gapped or Logically Isolated Storage
Some immutable backup implementations include:
- Network segmentation
- Separate management credentials
- No domain integration
- Separate authentication boundary
This reduces lateral movement risk.
Immutable backup is strongest when combined with identity separation.
Object Lock, WORM and Retention Policies Explained
To properly evaluate immutable backup, IT managers must understand terminology.
WORM (Write Once Read Many)
WORM storage ensures data can only be written once and read multiple times.
Once written, it cannot be modified.
Immutable backup leverages WORM principles to protect restore points.
Governance Mode vs Compliance Mode
Many object storage platforms provide:
- Governance mode
- Compliance mode
In governance mode, privileged users may override retention under strict policy.
In compliance mode, no user can remove retention until expiry.
For ransomware defence, compliance mode is generally stronger.
Legal Hold vs Time-Based Retention
Legal hold prevents deletion indefinitely until explicitly removed.
Time-based retention locks data until a specific date.
Immutable backup typically uses time-based retention aligned to recovery objectives.
Understanding these distinctions is critical for correct configuration.
Immutable Backup in Microsoft 365 and Azure
Many organisations assume Microsoft 365 provides full recovery protection.
It does not.
Microsoft provides availability and limited retention. It does not provide long-term immutable backup by default.
Third-party backup solutions are required to implement immutable backup for:
- Exchange Online
- SharePoint
- OneDrive
- Teams
Azure supports immutable blob storage, allowing backup repositories to apply retention locks.
Azure Backup vault immutability also provides protection for recovery points.
While immutable backup strengthens recovery posture, it must sit within a clearly defined business continuity vs disaster recovery framework to ensure operational resilience.
Immutable backup protects data restoration capability. It does not replace business continuity planning.
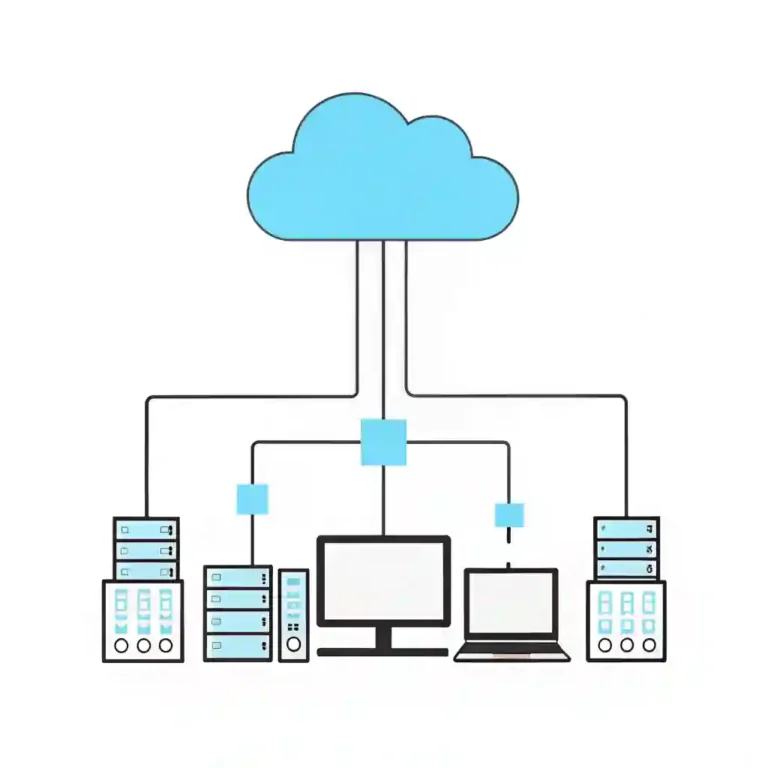
On-Prem vs Cloud Immutability
Immutable backup can be deployed in multiple ways.
On-Prem Hardened Repository
- Linux hardened repository
- No domain join
- Immutable flag applied
- Separate credential set
- Limited SSH access
This approach provides control and performance but requires strong governance.
Cloud Object Storage
- Azure Blob with immutability
- S3 object lock
- Independent storage account
- MFA enforced access
Cloud immutability offers scalability and offsite protection.
Hybrid Architecture
Best practice often combines:
- On-prem fast recovery
- Cloud immutable offsite copy
- Independent credential control
This layered design reduces risk concentration.
Implementation Considerations for IT Managers
Deploying immutable backup requires structured planning.
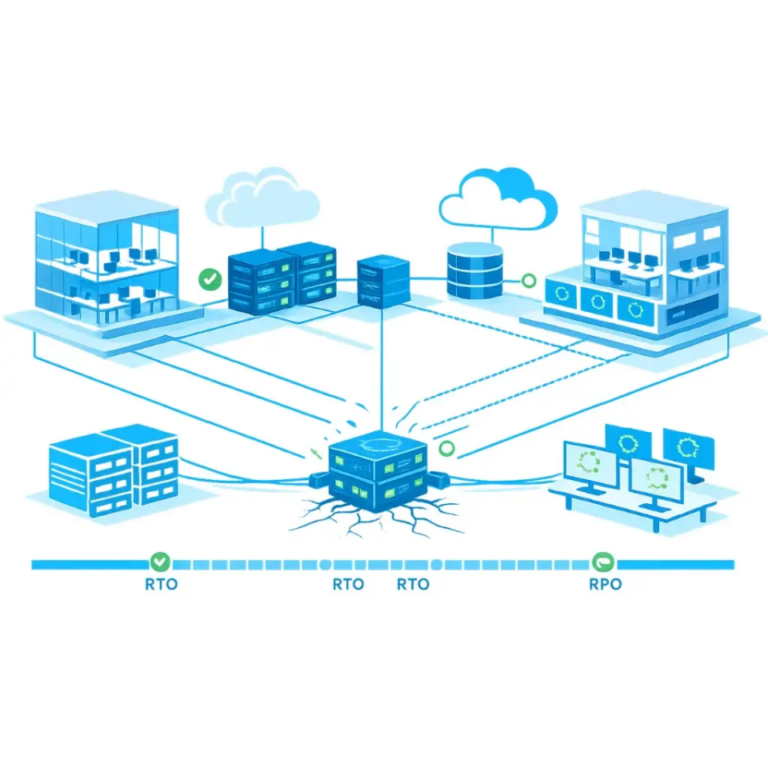
1. Align with RTO and RPO
Retention period must support recovery objectives.
If ransomware dwell time is estimated at 21 days, retention shorter than that may be insufficient.
2. Separate Backup Administration
Backup admin accounts should:
- Use MFA
- Be isolated from domain admin
- Have restricted scope
- Be monitored
Immutable backup is weakened if identity is compromised.
3. Storage Sizing
Longer immutability increases storage requirements.
IT managers must:
- Model growth
- Plan for retention expansion
- Monitor capacity
4. Network Segmentation
Backup repositories should not be flat-network accessible.
Segmentation reduces attack surface.
Immutable backup should form part of your wider IT resilience strategy, not operate as an isolated technical control.
Testing, Governance and Operational Control
Immutable backup is not effective unless tested.
Testing should include:
- Full restore simulations
- Granular file recovery
- Virtual machine restore
- Tenant-level restore (Microsoft 365)
Governance controls must include:
- Logging and monitoring
- Role-based access control
- Change approval workflows
- Quarterly validation
Without testing, immutable backup is theoretical protection.
Common Mistakes with Immutable Backup
Even technically capable teams make configuration errors.
Common issues include:
Retention Too Short
If immutability is 7 days and ransomware dwell time is 14 days, restore points may already be compromised.
No Secondary Copy
Immutable backup should not be the only copy.
Follow 3-2-1-1-0 principles:
- 3 copies
- 2 media types
- 1 offsite
- 1 immutable
- 0 restore errors
No Identity Hardening
If attackers compromise backup console identity before lock is applied, configuration may be altered.
Assuming Cloud Equals Immutable
Cloud storage is not automatically immutable.
Retention lock must be explicitly configured.
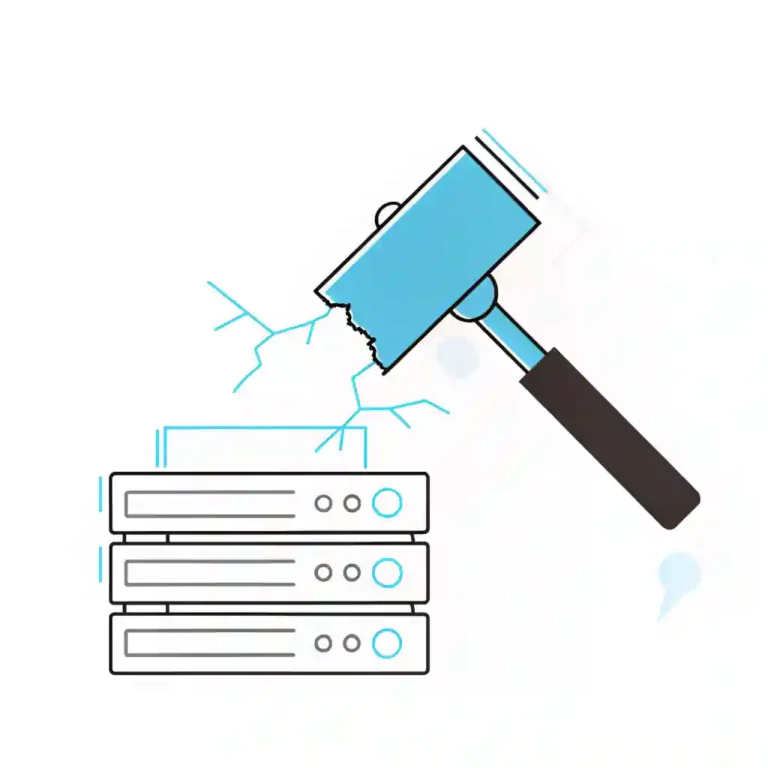
The Financial Impact of Not Implementing Immutable Backup
Ransomware recovery costs include:
- Incident response
- Legal advisory
- Downtime
- Regulatory reporting
- Reputational damage
- Infrastructure rebuild
Without immutable backup, recovery may require paying ransom or rebuilding from scratch.
The cost of prevention is almost always lower.
Don’t Let Your Backup Become Your Weakest Link
Backup used to be considered a routine operational control.
Today, it is a frontline security defence.
Immutable backup ensures that when attackers attempt to destroy recovery capability, they fail.
Before assuming your recovery posture is secure, review your complete IT resilience guide and ensure immutability, identity, segmentation and testing are aligned.
If you are unsure whether your backup environment is truly immutable, speak to Qual Limited.
We help IT managers across the UK design practical, layered resilience architectures that protect against modern threats.
Book a call with one of our account managers about the vast types Business IT Services today.
Ready to upgrade your IT?
Get the technology your business needs with our transparent pricing and expert support.
FAQs
What is immutable backup?
Does Microsoft 365 include immutable backup?
Is immutable backup expensive?
How long should immutability be configured?
Can ransomware delete immutable backup?
Next Steps
If your backup environment can be deleted by an admin account, it is not fully protected.
Immutable backup is no longer optional for modern IT environments.
Define your retention.
Separate your identities.
Test your recovery.
Qual Limited can review your backup architecture and identify whether immutability is properly configured.